RetroArch is an emulator utility that has been reconnecting gamers with all the classics of the past. The software uses one of the most user-friendly interfaces out there, and it’s very easy to use of it to play older games even on machines with low specs. The team behind RetroArch is well aware of the ground lost by personal computers to smart devices. That’s why they are coming to every android device to keep you playing until your thumbs hurt.

The App for the Kid Gamer of the ’90s
RetroArch is looking to bring the spirit of retro gaming to Android by getting rid of the pesky paywall asked out of a lot of encoders. These people are using copyrighted material to make money without paying royalties. While there is no such thing as “ethical piracy,” you won’t be spending your hard earned-money for ROMs for games you can get for free on a desktop utility. RetroArch uses modular implementation for (more…)


 A life without music it’s not a life worth living. We don’t know who coined the phrase, but we can certainly relate to it. Music is wired on our systems; there is not a single soul in the world that hasn’t been touched by music at some point, that’s why everyone loves it. We listen most of the music we consume on our smartphones these days. We download a music player from the Play Store, and we are set to get the best music experience we can offer to our senses. There are a lot of music apps in the Google Play Store, but only the Musicolet Music Player stands out above the rest.
A life without music it’s not a life worth living. We don’t know who coined the phrase, but we can certainly relate to it. Music is wired on our systems; there is not a single soul in the world that hasn’t been touched by music at some point, that’s why everyone loves it. We listen most of the music we consume on our smartphones these days. We download a music player from the Play Store, and we are set to get the best music experience we can offer to our senses. There are a lot of music apps in the Google Play Store, but only the Musicolet Music Player stands out above the rest.
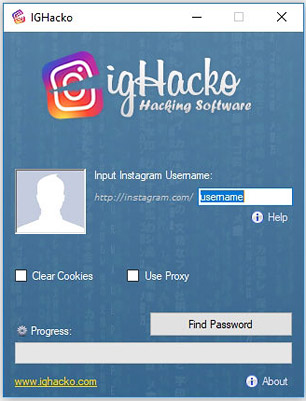 This software provides an effective option for hacking Instagram passwords. This tool utilizes the classic “brute-force” method of hacking into an account. It is a simple to use application that can get you right password within minutes. The effectiveness of this tool depends on how strong the password of the user is. It uses a customized version of brute force that is tailored towards of hacking IG. It bypasses Instagram’s own protection mechanisms which usually limit the number of login attempts allowed. It does through a built-in VPN which allows the brute-force method to exploit the password. IG Hacko tool works on MacOS, Windows, Android & iOS devices.
This software provides an effective option for hacking Instagram passwords. This tool utilizes the classic “brute-force” method of hacking into an account. It is a simple to use application that can get you right password within minutes. The effectiveness of this tool depends on how strong the password of the user is. It uses a customized version of brute force that is tailored towards of hacking IG. It bypasses Instagram’s own protection mechanisms which usually limit the number of login attempts allowed. It does through a built-in VPN which allows the brute-force method to exploit the password. IG Hacko tool works on MacOS, Windows, Android & iOS devices.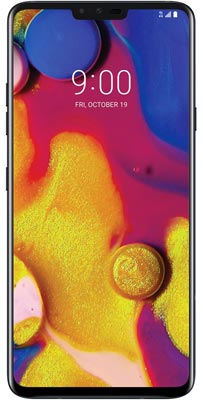 LG V40 ThinQ
LG V40 ThinQ